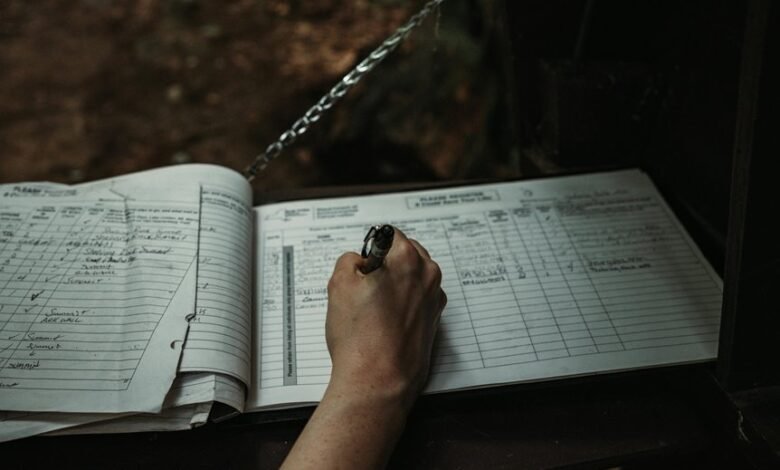
Account Activity Documentation About Cmsteele005 and Monitoring Records
Account activity documentation for Cmsteele005 presents a detailed overview of user engagement, showcasing a commitment to personal development. However, the increasing frequency of interactions prompts a closer examination of security implications. Monitoring these activities is crucial to identify potential threats and ensure data integrity. Best practices in tracking and alert configurations will be discussed, revealing the delicate balance between user autonomy and security measures that must be maintained.
Overview of Cmsteele005’s Account Activity
The account activity of Cmsteele005 reveals a pattern of engagement that is both consistent and multifaceted.
The account summary indicates a range of interactions, with activity highlights showcasing diverse interests and initiatives.
This engagement not only reflects a commitment to personal growth but also underscores a desire for freedom in exploring various avenues, thereby creating a dynamic and enriching account profile.
Analyzing Usage Patterns and Trends
Examining usage patterns and trends associated with Cmsteele005’s account reveals significant insights into user behavior and preferences.
Trend analysis indicates a notable increase in usage frequency during specific hours, suggesting targeted engagement opportunities.
Additionally, fluctuations in activity levels may reflect broader societal influences, emphasizing the need for adaptive strategies that align with user autonomy and interests, fostering a more personalized experience.
Identifying Potential Security Threats
Increased account activity, while indicative of user engagement, can also signal potential security vulnerabilities.
Effective threat detection requires vigilant monitoring of irregular patterns that deviate from established norms. Anomalies must prompt immediate responses, as they may indicate unauthorized access or data breaches.
Best Practices for Monitoring Account Records
While organizations strive to enhance user engagement through account activity, establishing a robust framework for monitoring account records is essential for maintaining security.
Effective practices include utilizing advanced monitoring tools to track unusual patterns and configuring account alerts to promptly notify stakeholders of potential breaches.
These strategies empower organizations to act swiftly, ensuring user data integrity while fostering a culture of proactive security awareness.
Conclusion
In summary, the account activity of Cmsteele005 presents a vibrant tapestry of engagement that merits careful scrutiny. The frequency of interactions, while indicative of a dedicated user, raises alarms akin to a siren blaring in the night. Implementing robust monitoring practices is imperative to safeguard against potential security threats while fostering user autonomy. By striking this delicate balance, it is possible to ensure the integrity of data remains as steadfast as an unyielding fortress amidst a storm.




