Contact Vision Start 845-836-2040 Revealing Phone Trace Discovery
Contact Vision Start 845-836-2040 frames phone trace discovery as a disciplined practice. It outlines how network data, device identifiers, and carrier signals can reveal origin while enforcing privacy safeguards. The approach emphasizes transparency, data minimization, and documented accountability. Clear procedures govern timing, permissions, and scope. The method balances legitimate inquiry with rights protection, presenting a structured path forward. Yet questions remain about practical limits and real-world application. The next step may redefine expectations.
What Is Phone Trace Discovery and Why It Matters
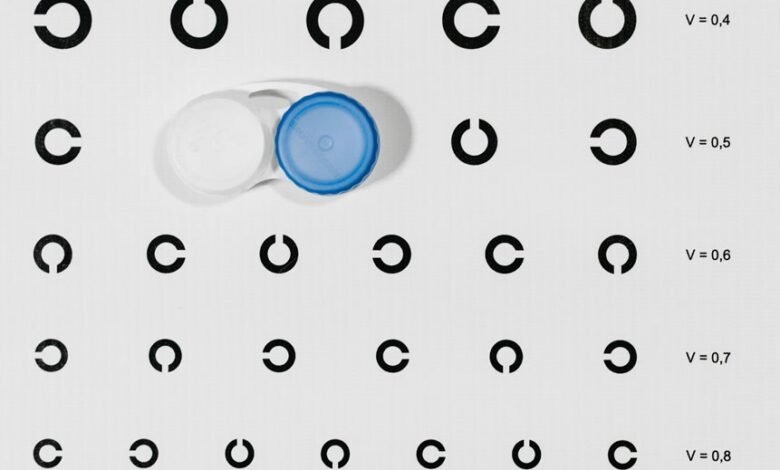
Phone trace discovery refers to the process of identifying the origin of a phone call or message by analyzing digital or network data.
The topic centers on accountability and impact, guiding policy and practice.
It emphasizes discovery ethics and privacy safeguards, ensuring lawful access, minimization, and transparency.
Clarity supports informed navigation of consent, rights, and legitimate investigations within digital communication ecosystems.
How Modern Tracing Tech Reveals Caller Details
Modern tracing technologies combine network metadata, device identifiers, and carrier signals to reveal caller details with increasing precision.
The approach emphasizes data minimization and traceability, aligning with lawful use.
Analysts assess data quality to ensure tracer accuracy while minimizing exposure.
Caller privacy concerns shape safeguards, encouraging transparent practices and verifiable methodologies that balance investigative needs with individual rights and societal trust.
Timing, Permissions, and Privacy: Rules That Shape Tracing
Timing, permissions, and privacy govern tracing activities by establishing when data can be collected, who may access it, and how protections are implemented.
The framework emphasizes timing permissions and privacy rules to curb misuse while enabling legitimate inquiry.
It presents a balanced approach, ensuring lawful access, transparent processes, and robust safeguards, guiding stakeholders toward responsible, liberty-preserving data practices within traceable communications.
Real-World Scenarios: From Mystery Calls to Practical Next Steps
Real-world tracing scenarios illustrate how theoretical timing and privacy frameworks apply to everyday inquiries.
In practice, investigators map call tracing steps to actionable outcomes, assessing caller intent and risk while preserving user rights.
Clear procedures guide next steps: verify sources, document evidence, and communicate limits.
Address privacy concerns through transparent scope, minimal data use, and proportionate responses, enabling informed, autonomous decisions.
Conclusion
In the end, Phone Trace Discovery hinges on disciplined methods and ethical guardrails. By combining network data, device identifiers, and carrier signals, investigators can identify origins without sacrificing privacy. Clear timing, permissions, and scope prevent overreach and protect rights. Real-world applications—from mystery calls to actionable follow-ups—demonstrate the approach’s value. It’s a ledger, not a weapon; transparency keeps trust, and accountability ensures every trace serves legitimate inquiry, like a lantern guiding cautious steps through fog.




