User Activity Documentation Covering Anoceligt and Alerts Logs
User activity documentation plays a crucial role in enhancing security management. Anoceligt logs capture specific user interactions, while alerts logs provide real-time insights into potential threats. Together, they help identify anomalies and trends that may signal security breaches. Understanding the interplay of these logs can lead to improved security strategies. However, the effectiveness of such documentation hinges on best practices that are often overlooked. What are these practices, and how can they be implemented?
Understanding Anoceligt Logs
Understanding Anoceligt logs requires a careful examination of their structure and function within the broader context of user activity documentation.
Various anoceligt log types serve distinct purposes, capturing specific user interactions. Log retention policies dictate how long these records are preserved, balancing the need for detailed oversight with individual privacy rights.
This careful management fosters an environment conducive to both security and user autonomy.
The Role of Alerts Logs in Security
Alerts logs play a pivotal role in enhancing security measures within user activity documentation.
Their alert significance lies in providing real-time insights into potential threats, facilitating proactive security monitoring. By analyzing these logs, organizations can identify anomalies, respond swiftly to incidents, and fortify defenses.
Consequently, alerts logs contribute to a comprehensive security framework, empowering users with the freedom to operate in a safer environment.
Analyzing User Activity Patterns
How can organizations effectively discern user behavior to enhance security protocols?
By analyzing activity trends, organizations can identify anomalies indicative of potential security breaches. This analysis reveals patterns in user behavior, enabling proactive measures to mitigate risks.
Understanding these trends not only strengthens security protocols but also fosters a culture of awareness and responsibility among users, ultimately promoting a safer digital environment.
Best Practices for Effective Documentation
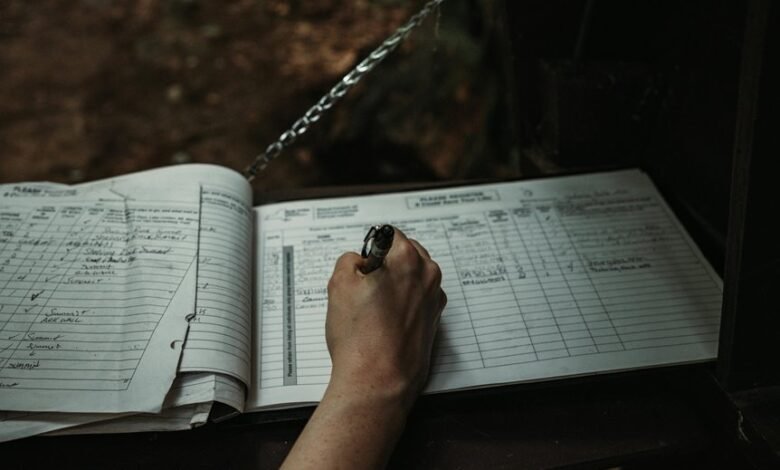
Effective documentation serves as a cornerstone for successful user activity analysis and security enhancement.
Employing effective strategies such as maintaining clear, concise records and adhering to established documentation standards ensures that logs are useful, accessible, and actionable.
Regular reviews and updates further enhance clarity, enabling users to respond promptly to alerts while fostering an environment of transparency and accountability in user activity management.
Conclusion
In conclusion, effective user activity documentation through Anoceligt and alerts logs is crucial for enhancing an organization’s security posture. While some may argue that such logging can feel invasive, it is essential to recognize that these practices promote a culture of accountability and awareness. By embracing comprehensive documentation, organizations not only safeguard their digital environments but also empower users to take an active role in protecting sensitive information, ultimately fostering a collaborative approach to security.




